Security by Design for IoT Devices
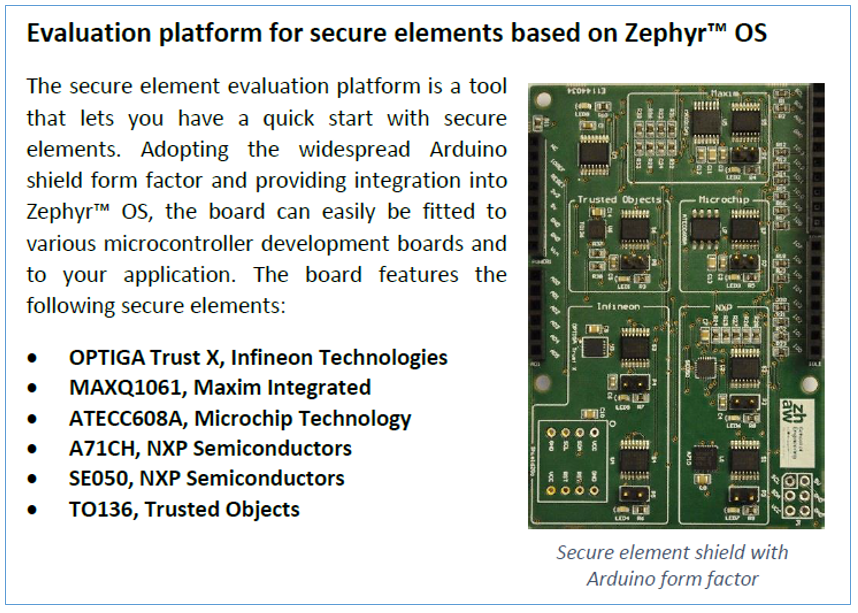
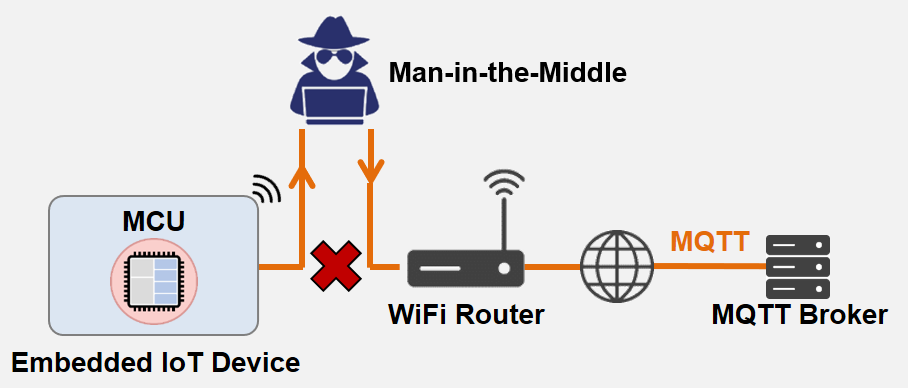
A new Whitepaper shows how to apply a systematic design process to protect your IoT devices. Unprotected IoT devices are an easy target for cyber-attacks. The ZHAW Institute of Embedded Systems has published a Whitepaper that describes the application of a systematic development process to identify threats, derive security requirements and implement effective protection measures. […]